While firewall and AV solutions are still useful, APTs are known to bypass them with ease, whether it be by abusing digital certificates, using trusted domains for C2, exploiting a zero-day vulnerability, or a good old-fashioned socially engineered spear phishing campaign. As a result, cybersecurity vendors have been developing new “next generation” solutions capable of detecting APT attacks.
Unfortunately, the mean time to detect (MTTD) a breach is still 197 days, Ponemon Institute & SANS reported in June 2019. In order to reduce MTTD, many cybersecurity vendors are developing AI-integrated solutions. In order to let others gain a deeper understanding of our tech, CyCraft Senior Researcher, C.K. Chen spoke at Code Blue 2019 and “lifted the curtain” behind one of his team’s design processes on overcoming the design challenges of a threat hunting machine learning model, a possible solution to reducing MTTD. Fuchikoma, the ML model C.K. discussed, is a simplified variant of just one of our 50+ ML learning models that we at CyCraft use in our CyCarrier platform.
“As the rate of cyberattacks increases, so does the need for cooperation between civilian, corporate, and government organizations. My team and I want to do our part and share some of the intuition behind how CyCraft defeats APTs, via an open source demonstration of a working threat hunting machine learning model.”
-C.K. Chen, CyCraft Senior Researcher
We at CyCraft are proud to be the first Taiwanese cybersecurity vendor to join the
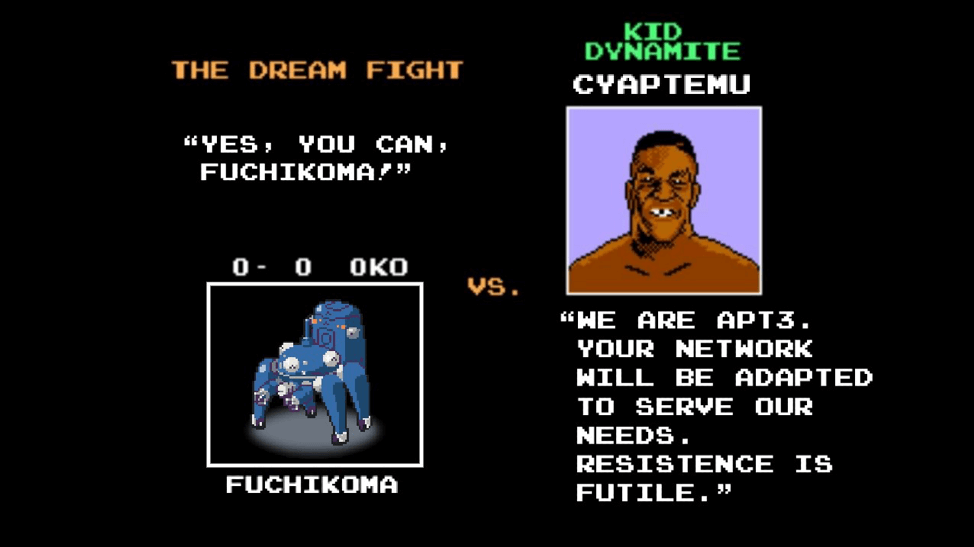
MITRE ATT&CK Evaluations. While we are ready and confident to join the second round of evaluations, we were unable to join the first round of evaluations as our platform was still nascent (CyCraft was less than a year old then). In preparation for the round 2 evaluations, C.K. Chen and team went about designing an emulation of APT3, which they creatively named CyCraft APT Emulator or CyAPTEmu for short.
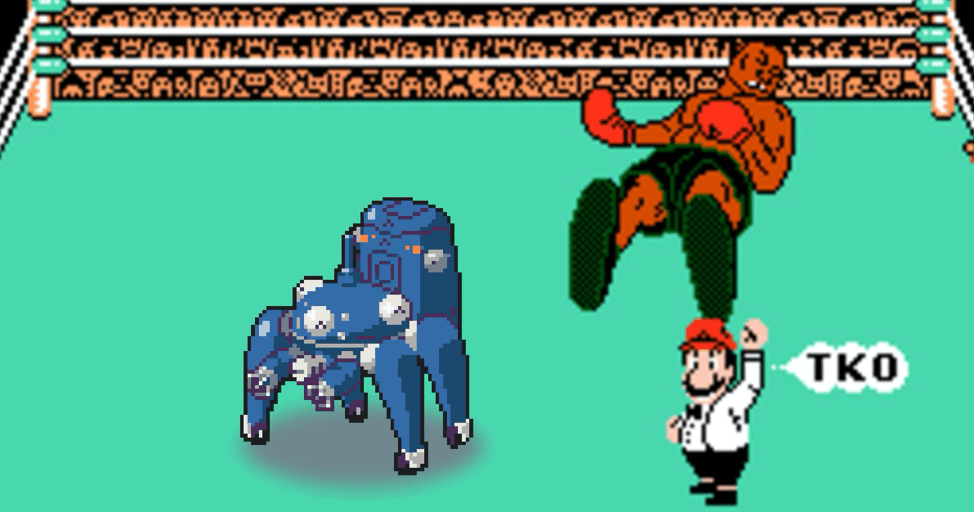
Our Fuchikoma is a proof of concept system for demonstrating some of the ideas behind the autonomous threat hunting that we use at CyCraft. Naming-wise, more North Americans are familiar with the Tachikomas that appeared in the 2002 anime TV series Ghost in the Shell: Stand Alone Complex. Fuchikomas are from the original Japanese manga, but both are four-legged walker tanks endowed with artificial intelligence. In the show, Fuchikomas are self-sufficient; however, they reach peak performance when paired with a human operator. In this way, Fuchikoma mirrors our own design philosophy; the best cyber defense is a hybrid of artificial intelligence and human ingenuity.
Indeed, our experienced team of security analysts work with our
CyCarrier platform to deliver quality cybersecurity to clients among the Fortune Global 500, national governments, critical infrastructure, banking, telecommunications, ICS, SMEs and more. In just two years, we have seized the domestic market and have been expanding rapidly across Asia. We have been nominated for the
“Most Innovative Cybersecurity Company” in the Cybersecurity Excellence Awards 2020.
CyCraft is more than buzzwords. We show evidence, reveal case studies, and give back to the cyber community. This article is the first in a multi-part series about how our Senior Researcher C.K. Chen and team step-by-step used open source software to successfully design a working threat hunting machine learning model, which we called Fuchikoma. The development of CyAPTEmu, the APT3 emulator, will be covered in another article.