Before we introduce our fighters, let’s take a brief moment to acknowledge C.K. Chen, Cybots Senior Researcher and the lead designer (and trainer) of both Fuchikoma (the threat hunting machine learning model) and CyAPTEmu (the APT emulator).
C.K. attended National Chiao Tung University (QS ranked in the top 100 CS programs in the world, and second in Taiwan) where he received his PHD in Distributed Systems & Network Security, specializing in reverse engineering malware, malware analysis, and vulnerability discovery. He founded his university’s first CTF team, BambooFox, and participated in the 2016 and 2018 DEFCON Finals. In his free time, C.K. is a reviewer for HITCON and HITB and also lectures at the AIS3 “Hacker College” from time to time. For the last year, he’s been leading the research team at CyCraft, the first Taiwanese cybersecurity vendor to join the MITRE ATT&CK Evaluations.
Determined to do well in the second round of MITRE ATT&CK Evaluations against APT29, C.K. and team developed an emulation of the first round adversary – APT3.
C.K. attended National Chiao Tung University (QS ranked in the top 100 CS programs in the world, and second in Taiwan) where he received his PHD in Distributed Systems & Network Security, specializing in reverse engineering malware, malware analysis, and vulnerability discovery. He founded his university’s first CTF team, BambooFox, and participated in the 2016 and 2018 DEFCON Finals. In his free time, C.K. is a reviewer for HITCON and HITB and also lectures at the AIS3 “Hacker College” from time to time. For the last year, he’s been leading the research team at CyCraft, the first Taiwanese cybersecurity vendor to join the MITRE ATT&CK Evaluations.
Determined to do well in the second round of MITRE ATT&CK Evaluations against APT29, C.K. and team developed an emulation of the first round adversary – APT3.

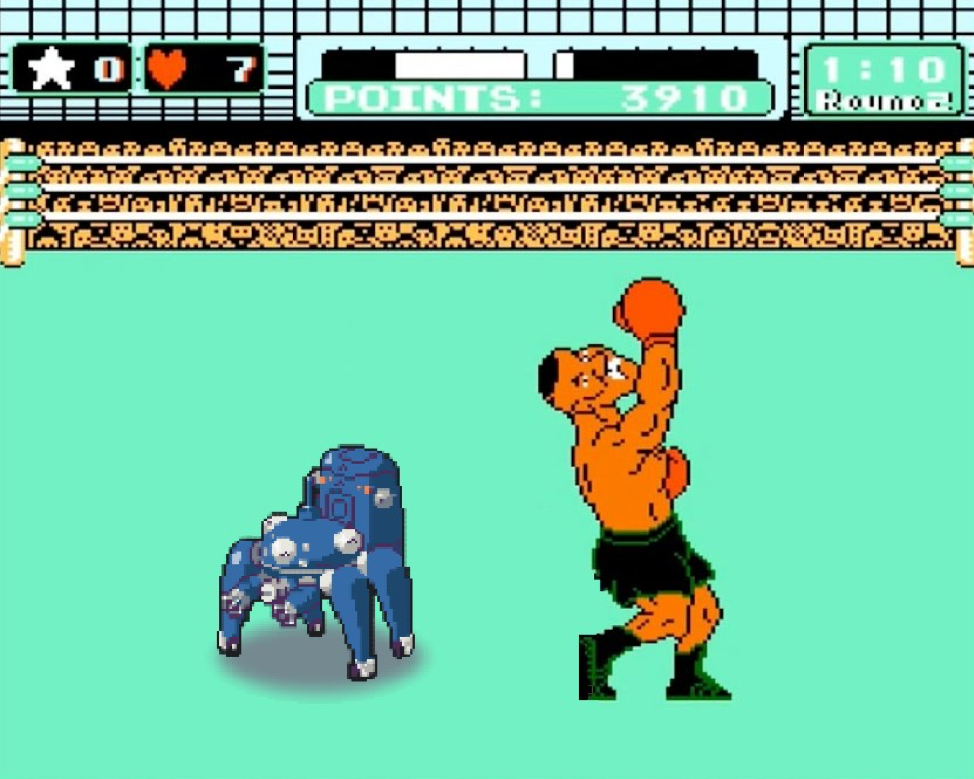
Caption: CyCraft presents: The Dream Fight Weigh In! ML Fuchikoma prepares to face off against the ruthless opponent, CyAPTEmu!
This is Part 2 in a multi-part series of articles about how CyCraft Senior Researcher C.K. Chen and team step-by-step used open source software to successfully design a working threat hunting machine learning model. We suggest starting from Part 1: Introducing Fuchikoma.